iOS Code Signing Tutorials
This is Part-3 of the iOS Code Signing tutorial series. This series covers fundamentals of the iOS code signing process. You can find all the posts in the series linked below
- iOS Code Signing: 1. Getting Started
- iOS Code Signing: 2. Certificate Signing Requests
- iOS Code Signing: 3. Certificates
- iOS Code Signing: 4. Provisioning Profiles
- iOS Code Signing: 5. Signing iOS App
*******************************************************
iOS Code Signing: Certificates
In the previous post, we have covered how to generate the Certificate Signing requests from Keychain Access as well as from using command line tools. In this post, we will cover how to generate certificates for iOS development and we will look inside the certificate contents. As an iOS developer, you must have created certificates by yourself at least once and stored in the keychain. You probably never looked at it until your Xcode tells you that your certificate expired. It’s important to understand the certificate contents in order to understand the code signing process. Now, let’s dive deep into Certificates.
The certificate is at the core at code signing in iOS apps. Let’s forget about Apple Certificates and get into real life. When you finish university or some professional course then you get Certificate. You then attach that certificate to your CV or LinkedIn profile to show that you are trusted by some authority ( University) that you have completed that programme and you have knowledge. The employer then gets impressed and offer you the job. Certificates are more powerful when they are offered by popular trusted authorities. If you get the certificate from London Business School, Oxford or Cambridge University then people trust you more. Basically, it’s the same concept in iOS or Apple world.
In the iOS world, you get the certificate from trusted authority a.k.a Certificate Authority (CA) which is Apple who certifies that
- You are legitimate (not necessarily good) developer of the app.
- You also paid Apple to get membership Apple Developer or another similar programme.
- Apple has verified that all the information provided by is correct and issued you a certificate to build an awesome iOS apps.
Getting the certificate from Apple isn’t a big thing, you just have to pay them enough to get those required certificates. However, understanding the details of certificates and why we need those certificates are definitely the big thing. Apple has ten different types of the certificates as mentioned in the official documentation here. Each certificate has a different purpose but there are two main certificates i.e Development Certificate and Distribution Certificate.
Create Certificates
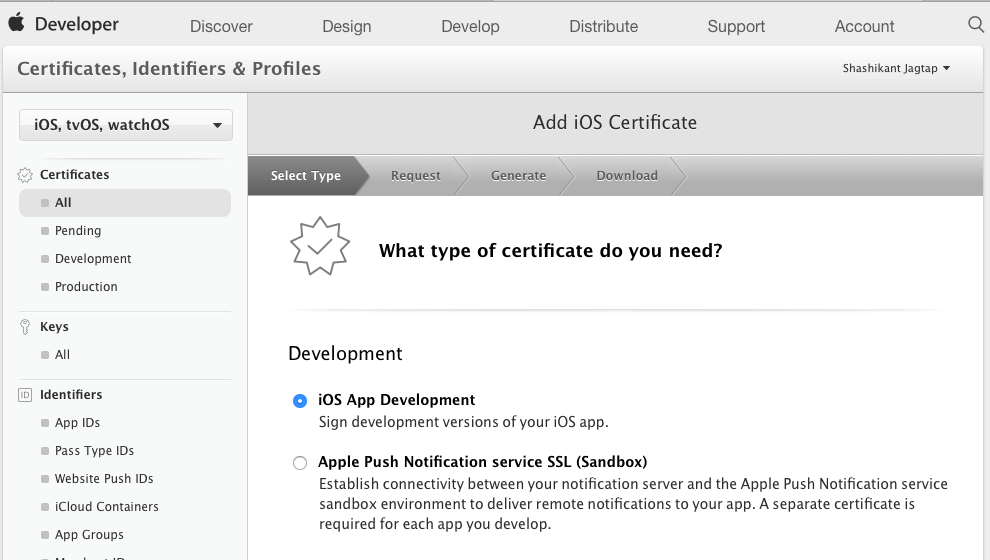
Let’s go through the process of generating the certificates. In order to generate a new certificate, we have to log in to our developer portal and select the Certificates and Profile section. If you click on Certificates section, you will see an option in the form of a + button to create a new certificate. Click on the add new certificate which prompt you to select the type of certificate that you want to create as shown below.
After selecting certificate in this case “iOS App Development”, the next step will be to create CSR which we have seen in the above session. Apple will give all the instructions to generate CSR file locally.
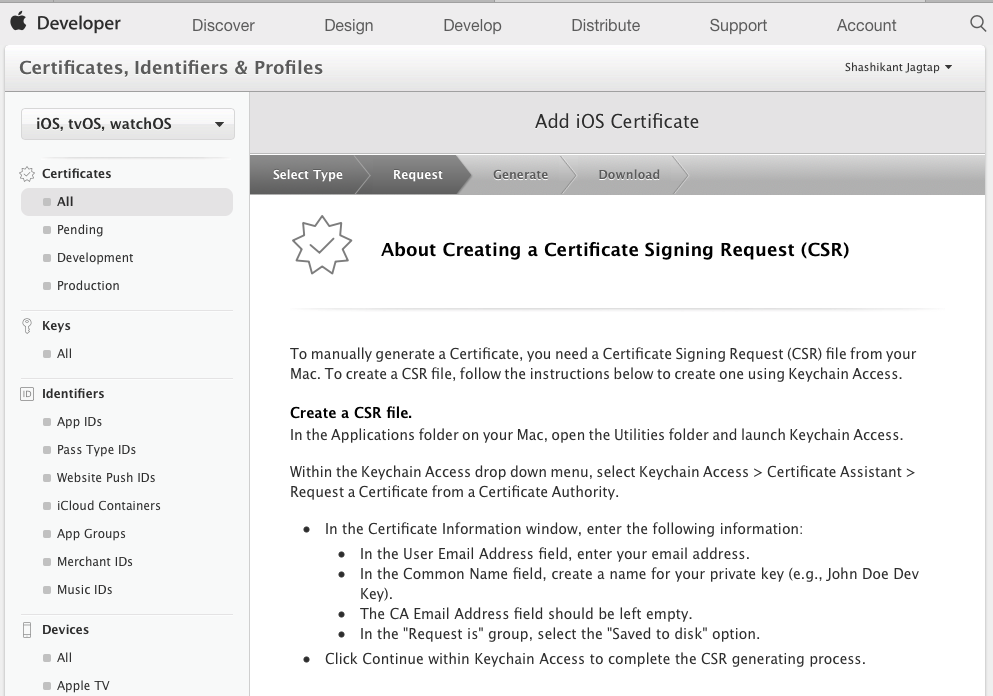
This will ask you save the file CertificateSigningRequest.certSigningRequest on your local machine. The next screen we need to upload this file to developer portal to get the certificate. We can then download the certificate to the local machine.
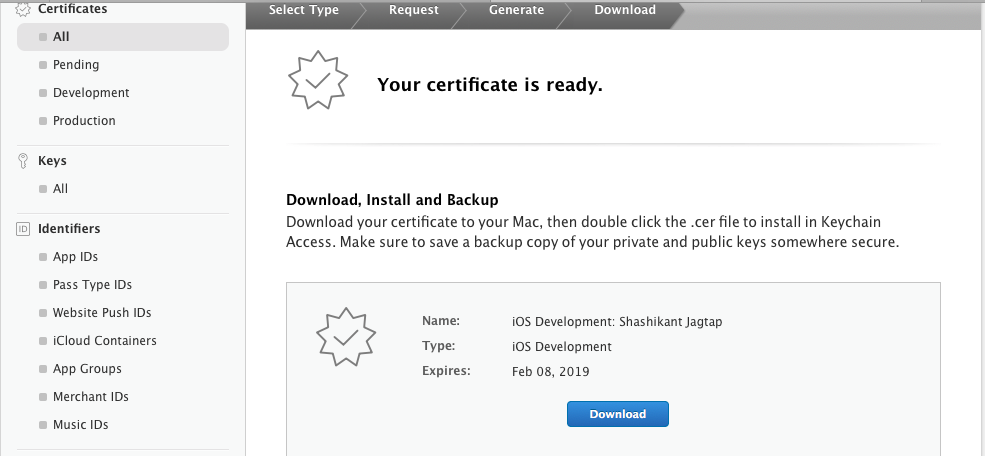
At this stage, you will have the file with .cer extension downloaded to your local machine. You can then double click on the certificate to add it to the keychain. Verify the Keychain has newly generated certificate with private key attached as shown below
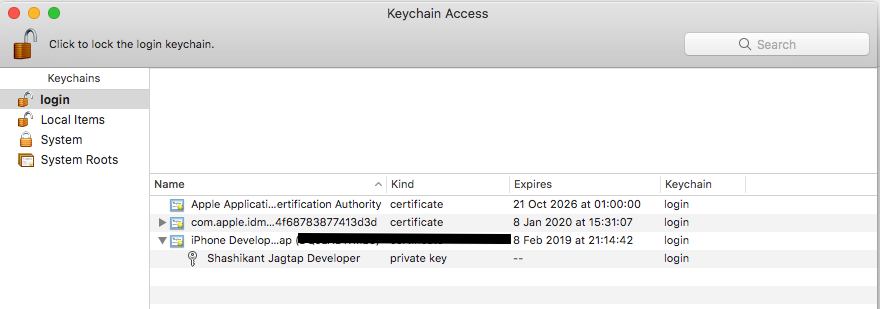
If you see the certificate with the private key in the keychain then you can confirm that you have successfully generated iOS developer certificate. You can also confirm that using the following command.
$ security find-identity -v -p codesigning
This command will print all the certificates that you have on the keychain.
You can generate the same for the distribution as well using a similar process but selecting iOS distribution instead of iOS App development in the certificate type.
Explore Certificate
Now that we have successfully generated the certificate for iOS Development, let’s look at the certificate and see whats inside to get more information.
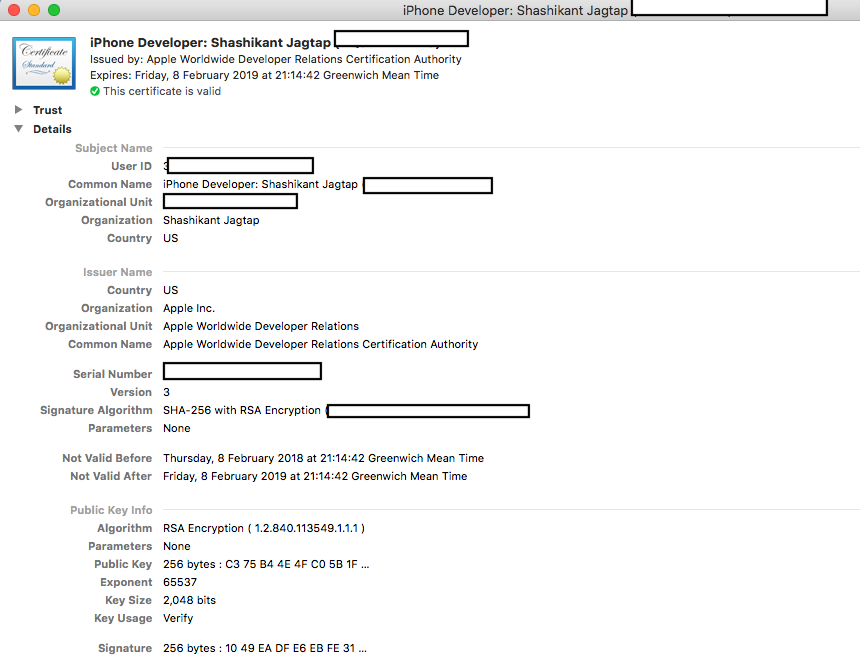
Basically, the certificate has all the data that we have provided during creating certificate signing request, Apple then adds some signer data like Authority, expiry date etc. The whole certificate has the signature attached to it. In the Keychain application if you right click on the certificate and “Get Info” then you will see all this information. It should have following things
- Subject Name: This contains UserID, name, organisation details and the country name of the developer.
- Issuer name: This contains Apple details like authority, organisation unit that has issued the certificate and expiry date of the certificate.
- Public Key Info: This contains details of the public key like which algorithm and signature are used.
- Fingerprints: Finally it contains fingerprint details like SHA-256 and SHA-1 etc. The certificate also shows the purpose of what this certificate will be used for like codesigning or any other activity.
You can see the certificate details from the command line as well.
$ openssl x509 -in ios_development.cer -inform DER -text -noout
This will show exactly the same information on the command line with the whole signature at the bottom.
Note that, these details are exposing all the information of the certificate itself but we also need private key attached to the certificate to code signing the apps. This is where we need the certificate in the P12 format to back it up with the private key.
PKCS#12
In Cryptography, PKCS#12 a.k.a Public Key Cryptography Standard is the standard used to store private keys with public key certificates protected with the password. This format defines multiple cryptographic objects in the single file.
In our case in the iOS Development certificate, we can export the certificate from keychain into the Personal Information Exchange a.k.a p12 format. Just right-click on the certificate in the Keychain Access and select Export.
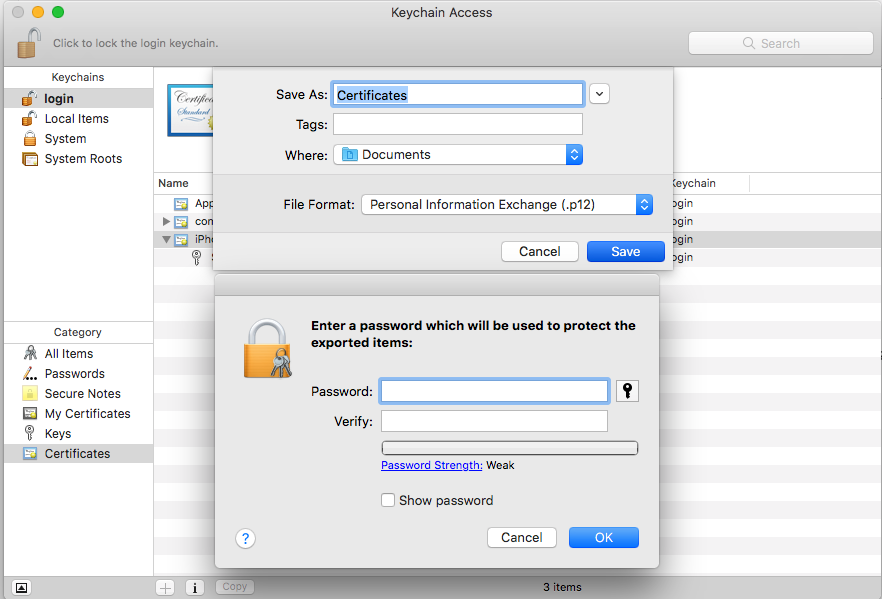
You will see that option to export your certificate in the .p12 format also you can encrypt this certificate with a strong password.
You can also create the certificate in the .p12format using the command line. If you have generated the private key using command line while creating CSR as mention above then we can use this key.
$ openssl x509 -in XXXXX.cer -inform DER -out mycert.pem -outform PEM $ openssl pkcs12 -export -inkey my.key -in mycert.pem -out mycert.p12
If you provided the passphrase then this command will prompt you to enter the passphrase and you will see your certificate generated in the p12 format. Once, we have generated the certificate in .p12 format, it’s easy to backup. There is no risk of losing the private key while using on multiple Macs. The certificate in the p12 format has both your certificate combined with the private key. If you are interested to know whats inside the P12 certificate, you can find the details using the following command.
$ openssl pkcs12 -info -in mycert.p12
This will prompt you for the password if the p12 is encrypted. The storage container for PKCS#12 called safe bags which stores information as bags with each bag has its own attributes and actual content. In our case, we have two bags one for certificate and other for the private key. You will see bag attribute followed by the actual content of certificate or private keys.
At this stage, we understand the iOS certificates and it’s internal details. However having certificate alone can’t code sign iOS apps, it requires the private key to code sign the iOS apps. In the next part, we will see another important aspect of code-signing that are provisioning profiles and entitlements.

